Ultimate IoT implementation guide for businesses
IoT can offer many benefits to the enterprise, but it can be a challenge to implement. Learn the requirements and use best practices for a successful deployment.
The internet of things provides organizations with real-time information and business insights that, when acted upon, can make processes and operations more efficient and safer. IT administrators, architects, developers and CIOs considering an internet of things deployment must have a thorough understanding of what the internet of things is; how it operates; its uses, requirements, and tradeoffs; and how to implement internet of things devices and infrastructures.
What is IoT?
The internet of things (IoT) is a network of dedicated devices -- called things -- deployed and used to gather and exchange real-world data across the internet or other networks. Examples of this technology in operation include the following:
- Cardiac patients have a heart sensor installed after surgery that reports diagnostic information about their heart function to a monitoring physician.
- Homes use sensors for tasks including security and home management, such as lights and appliance control, with status reporting and control performed through smartphone apps.
- Commercial buildings known as smart buildings use sensors to reduce power consumption, enhance safety and security and lower maintenance costs.
- Farmers use moisture sensors throughout the fields to direct irrigation where crops need it most.
- Ranchers use location sensors placed on each head of cattle to both identify and locate cattle across the ranch.
- Industrial plants use sensors to monitor the presence of dangerous materials or workplace conditions and to manage employee movement throughout the facility.
- So-called smart cities deploy a fleet of sensors to monitor road and traffic conditions, adjusting a traffic control apparatus dynamically to route and optimize traffic based on prevailing situations.
Key concepts of IoT are as follows:
A focus on real-world data. Where an enterprise routinely deals with documents, PowerPoints, images, videos, spreadsheets and many other forms of static digital information, IoT devices produce data that reflects one or more physical conditions in the real world. As an example, physical data can include actual manufacturing machine conditions derived from sensors and material workflows tracked by RFID tags across a factory floor. IoT devices help a business not only learn what's happening, but also exercise control over what's happening.
The vital importance of immediacy in real-time operation. Where routine data -- such as a memo document -- can exist for days or months without ever being used, IoT devices must deliver data for collection and processing without delay. This makes related factors, such as network bandwidth and connectivity, particularly important for IoT environments where the usefulness or relevance of data can be measured in seconds. For example, cardiac data from a heart patient or pressure data from a nuclear reactor must be delivered and processed immediately.
The resulting data itself. IoT projects are often defined by the larger project or business purpose driving IoT deployment. In many cases, IoT data is part of a control loop, with a straightforward cause-and-effect objective. For example, a sensor tells a homeowner that their front door is unlocked, and the homeowner can use an actuator -- an IoT device designed to translate control signals received from the network into real-world actions -- in the door to lock it remotely. Similarly, the data provided by sensors collecting telemetry from factory machines can be processed to find bottlenecks in maintenance and workflows, which can then be optimized to save time and money.
Scope of data and collection. The goal of IoT is to help businesses create a broad and detailed picture of an operational environment, such as a city highway system. Creating this picture takes many sensors of varying types and capabilities, including pressure, temperature, moisture and countless other parameters. IoT deployments can involve hundreds, thousands or tens of thousands of individual sensors used to collect and deliver data for processing and decision-making.
But IoT can support much larger and more far-reaching business goals. Millions of IoT sensors can produce vast quantities of raw data -- far too much for humans to review and act upon. Increasingly, large IoT projects are the core of big data initiatives, such as machine learning (ML) and artificial intelligence (AI) projects. The data collected from vast IoT device deployments can be processed and analyzed to make vital business projections or train AI systems based on the real-world data collected from vast sensor arrays. Those back-end analyses can demand substantial storage and computing power. Computing can be managed in centralized data centers, in public clouds or distributed across several edge computing locations close to where data is collected.
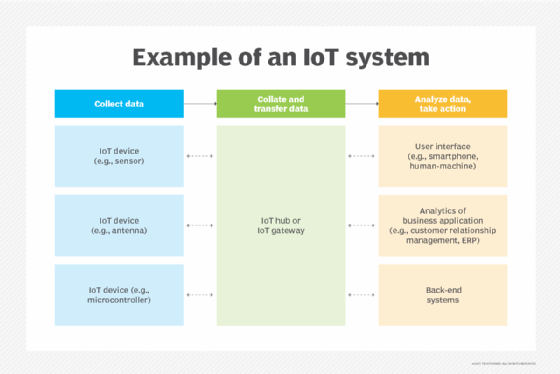
How does IoT work?
IoT isn't a single device, software or technology; it is an amalgam of devices, networks, computing resources and software tools and stacks. Understanding IoT terminology usually starts with the IoT devices themselves.
Things. Every IoT device -- a thing or smart sensor -- is a small, dedicated computer possessing an embedded processor, firmware and limited memory and network connectivity. The device collects specific physical data and sends that data out onto an IP network, such as the internet. Depending on the sensor's work, it might also include amplifiers, filters and converters. IoT devices are battery-powered, rely on wireless network connectivity through individual IP addresses and can be configured individually or in groups.
Connections. The data gathered by IoT devices must be transmitted and collected. This second layer of IoT involves the broad network, along with an interface between the network and back-end processing. The network is typically a conventional IP-based network, such as an Ethernet LAN or public internet. Every IoT device receives a unique IP address and unique identifier. The thing passes its data to the network using a wireless network interface, such as Wi-Fi, or a cellular network, such as 4G or 5G. As with any network device, data packets are marked with a destination IP address where the data is to be routed and delivered. Such network data exchange is identical to the everyday exchange of network data between ordinary computers. The destination for this raw sensor data is typically an intermediary interface, such as a local IoT hub or IoT gateway. The IoT gateway usually serves to collect and collate the raw sensor data, often applying early preprocessing tasks such as normalization and filtering to IoT data.
Back end. The enormous volume of real-time data produced by an IoT sensor fleet and collated at the IoT gateway must be analyzed to yield deeper insights, such as exposing business opportunities or driving ML. The IoT gateway sends its cleaned and secured sensor data across the internet to a back end for processing and analysis. Analyses are performed using extensive computing clusters, such as Hadoop clusters. This back end might be located at a corporate data center, a colocation facility or a computing infrastructure architected in the public cloud. There, the data is stored, processed, modeled and analyzed.
Interface. IoT plays a vital role in automation, providing data collection and computing power to help systems analyze, identify and react to issues far faster than humans ever could. However, every IoT system will also provide some form of human interface -- whether an alert, dashboard, big data reporting or other form -- intended to let human operators keep watch and check on the behaviors of the IoT infrastructure. As one simple example, a smart home needs an interface that lets the homeowner set the inside temperature and check the status of smart devices within the home.
What are the layers of an IoT architecture?
The discussion of sensor, connection and back-end layers can help business and IT staff understand IoT technology, but such discussion also demands consideration of IoT architecture. Although the scope and detail of an IoT architectural plan can vary depending on the IoT initiative, it's vital for leaders to consider how IoT will integrate into the current IT infrastructure.
There are four major layers in an IoT architecture. These layers possess a relationship like the Open Systems Interconnection networking model and can be discussed from bottom to top:
- Device layer. This layer represents the devices -- or things -- that translate the physical world into digital data and back again. Devices include sensors and actuators that might number into the hundreds of thousands for an IoT deployment. Each device connects to a network using wired or, more likely, wireless connections.
- Network layer. The network layer is responsible for connecting IoT devices and then moving IoT data and commands between devices and computing resources. The network layer includes IoT and network gateways and might also include some means of data aggregation or preprocessing, such as edge computing, to reduce the sheer amount of raw data exchanged across the network.
- Computing layer. This layer represents the local processing effort involved in IoT deployments. It's where IoT data is locally collected, stored and initially analyzed. This edge computing is where IoT data might be preprocessed, normalized and aggregated. Although it might be possible to perform most computing in the main data center, local computing layers can reduce network traffic and let data center resources focus on higher applications.
- Application layer. At the highest level, an application layer is responsible for handling user interactions, such as device management or environment control. However, the application layer is mainly where a primary data center ingests data delivered from the computing layer and performs detailed analytics and reporting on the IoT data.
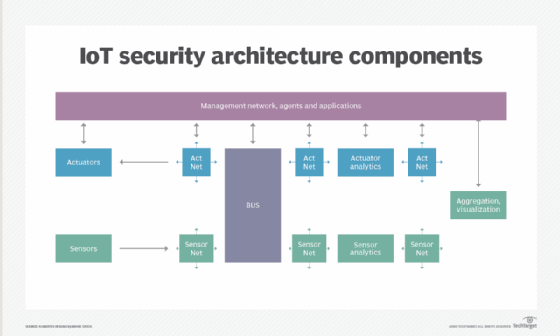
There are four major architectural issues to consider:
- Infrastructure. The physical layer includes IoT devices, the network and computing resources used to process the data. The infrastructure discussion often includes sensor types, quantities, locations, power, network interface and configuration and management tools. Networks involve bandwidth and latency considerations to ensure they can handle IoT device demands. Computing manages the analysis on the back end, and organizations might need to deploy extensive new computing resources to manage additional processing or use on-demand resources, such as the cloud. Infrastructure discussions also involve a careful consideration of IoT protocols and standards, such as Bluetooth, Global System for Mobile communication, 4G or 5G, Wi-Fi, Zigbee, narrowband IoT and low-power wireless personal area network.
- Security. The data produced by the internet of things can be sensitive and confidential. Passing such data across open networks can expose devices and data to snooping, theft and hacking. Organizations planning an IoT project must consider IoT privacy and the best ways to secure IoT devices and data in flight and at rest. Encryption is a common approach for IoT data security. Additional security must be applied to IoT devices to prevent hacking and malicious changes to device configurations. Security involves various software tools and traditional security devices, such as firewalls and intrusion detection and prevention systems.
- Integration. Integration involves getting everything to work together seamlessly, ensuring the devices, infrastructure and tools added for IoT will interoperate with an organization's existing systems and applications, such as systems management and ERP. Proper integration requires careful planning and proof-of-principle testing, along with a well-researched selection of IoT tools and platforms, such as Apache Kafka or OpenRemote.
- Analytics and reporting. The very top of an IoT architecture requires a detailed understanding of how IoT data will be analyzed and used. This is the application layer, which often includes the analytical tools, AI and ML modeling and training engines, and visualization or rendering tools. Such tools can be acquired from third-party vendors or used through cloud providers where data is stored and processed.
Business use cases for IoT
The vast array of small and capable IoT devices has found meaningful business applications in most major consumer, industrial, medical and government verticals. Consider some of the expanding use cases in five important industries:
- Home (commercial or end user). IoT devices appear in homes for energy management, security and even some task automation:
- Thermostats and lighting can be scheduled and controlled through internet applications.
- Motion-activated sensors can trigger video and audio streams to homeowner smartphones.
- Water sensors can watch basements for leaks.
- Smoke, fire and carbon dioxide detectors can report danger to users.
- IoT actuators can lock and unlock doors remotely.
- Smart refrigerators can track contents, and automated vacuums keep the home clean without direct human intervention.
- Manufacturing. IoT devices have found broad adoption in all manners of manufacturing and industrial settings. Examples of the industrial internet of things, or IIoT, include the following:
- IoT tags can track, locate and inventory enterprise assets.
- IoT devices can help monitor and optimize the use of energy, such as lowering lighting when human-occupied areas are idle or lowering temperature settings during off-hours.
- IoT sensors and actuators can support process automation and optimization.
- IoT devices can monitor all types of machine behaviors and parameters during normal operation, enabling ML to guide predictive maintenance in order to optimize process uptime.
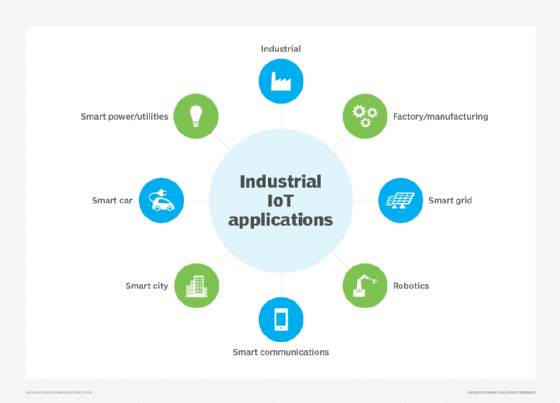
- Public/safety. IoT sensors with cellular-class connectivity can operate collaboratively across metropolitan areas to serve a wide range of purposes:
- IoT devices can detect the presence of vehicle traffic, enabling cities to adjust street lighting on idle streets and off-hours.
- Crime prevention efforts might include camera-based surveillance, while connected audio detection can direct police to areas where gunfire is detected.
- Cameras can be used to determine and optimize traffic, while transponders and cameras can read license plates or toll boxes to direct toll collection and management.
- Interconnected parking systems enable cities to track parking spots and alert drivers to available spots through an app.
- Sensors can watch bridges and other structures for stress and problems, enabling early detection and remediation.
- Sensors can monitor water quality, enabling early detection of contaminants or pollutants.
- Medical/health. IoT is present in remote patient telemetry and other medical uses:
- IoT exists in countless wireless, wearable devices, including blood pressure cuffs, heart rate monitors and glucometers. Devices can be tuned to track calorie expenditure against exercise goals, as well as remind patients of appointments or medications.
- IoT enables early-warning devices, such as fall detection, that alert health providers and family members and even provide location information for potential issues.
- The remote monitoring of IoT helps health providers track patient health and adherence to treatment plans, while enabling them to better correlate health issues with telemetry data.
- Hospitals can use IoT to tag and track the real-time location of medical equipment, including defibrillators, nebulizers, oxygen and wheelchairs.
- IoT in staff badges can help locate and direct staff more efficiently.
- IoT can help with other equipment control, such as pharmacy inventory, refrigerator temperatures and humidity and temperature control.
- IoT hygiene-monitoring equipment can help ensure that medical environments are clean and reduce infection.
- Retail. IoT and big data analytics have found extensive use in retail sales and physical store environments:
- IoT devices can tag every product, enabling automated inventory control, loss prevention and supply chain management so that retailers can place orders based on sales and inventory levels.
- Cameras and other surveillance technologies can watch shopper activity and preferences, helping retail stores optimize layouts and organize related products to maximize sales.
- IoT devices can support touchless and scanless checkout and payment, such as near field communication payment.

What are the business benefits of IoT?
When business leaders research and consider IoT adoption, it's easy to find lists that cite the benefits of IoT, such as more efficient operations and long-term cost savings. Although this can be true, such conversations are tangential to the principal overarching benefits of IoT: knowledge and insight.
Accurate and timely business decisions demand knowledge and insight that can be difficult or even impossible to obtain. Businesses rely on knowledge and insight each time a sales manager forecasts the next quarter's revenue or a production manager decides whether to shut down a key machine in a vital production line for routine maintenance. The stakes are far higher when state inspectors discover structural defects in long-neglected municipal infrastructure, or when physicians struggle to diagnose serious maladies and improve patient outcomes.
IoT provides better immediate knowledge through measuring and reporting specific real-world conditions. Through modern instrumentation, such as the thermostat in a home that measures current temperatures to control heating or cooling systems, the real-world condition can be examined and responded to in real time. If a heart rate monitor alerts an excessive heart rate, the patient can slow down and relax to lower the heart rate to an acceptable level, take appropriate medication, contact their physician for further guidance or even call for medical assistance. If a traffic monitoring system sees a backup on a major highway, it can update travel apps of the prevailing conditions and enable commuters to select alternate routes and avoid the congestion.
But the real power and benefits of IoT are the long-term insights it can provide to business leaders. Consider the vast number of IoT sensors that can be distributed throughout equipment, vehicles, buildings, factories, campuses and municipal areas that enable better long-term insight through advanced analytics -- the back-end computing processes capable of evaluating and correlating a huge quantity of unrelated data to answer business questions and make accurate predictions about future circumstances. The data collected can also be used to train ML models, supporting the development of AI initiatives that achieve a deep understanding of the data and its relationships.
For example, the varied sensors distributed in a vehicle or industrial machine can be analyzed to detect variations in operation and condition, which might suggest the need for maintenance or even predict an impending failure. Such insights enable a business to order parts, schedule maintenance or make proactive repairs while minimizing the disruption to normal operations.
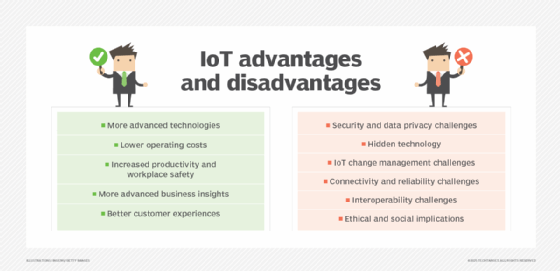
What are the challenges of IoT?
IoT projects can bring strong benefits to the business regardless of the deployment scope. But IoT can also pose serious challenges that a business must recognize and consider before undertaking any IoT project.
Project design. Although IoT devices readily implement a variety of standards, such as Wi-Fi or 5G, there are currently no significant international standards that guide the design and implementation of IoT architectures, and there's no rulebook to explain how to approach an IoT project. This allows for a great deal of flexibility in design, but it also allows for major design flaws, vulnerabilities and oversights. IoT projects should be led by IT staff with IoT expertise, but such expertise is constantly evolving. There is no substitute for careful, well-considered design and demonstrated performance based on copious testing and proof-of-principle projects.
Data storage and retention. IoT devices produce enormous amounts of data, which is readily multiplied by the number of devices involved. That data is a valuable business asset that must be stored and secured in accordance with proper compliance and retention requirements. And unlike traditional business data, such as emails and contracts, IoT data is highly time-sensitive. For example, a vehicle's speed or road data conditions reported yesterday or last month might have no timeliness today or next year. This means IoT data might possess a radically different lifecycle than traditional business data. This requires a significant investment in storage capacity, data security and data retention/lifecycle management.
Network support. IoT data must traverse an IP network, such as a LAN or the public internet. Consider the effect of IoT device data on network bandwidth and ensure that adequate, reliable bandwidth is available. Congested networks with dropped packets and high latency can delay and jeopardize the timeliness of IoT data. This might involve some architectural changes to the network and the addition of dedicated networks. For example, rather than pass all IoT data across the internet, a business might opt to deploy an edge computing architecture that stores and preprocesses the raw data locally before passing only curated data to a central location for analysis.
Device and data security. IoT devices are small computers connected to a common network, making them vulnerable to hacking and data theft. IoT projects must implement secure configurations to protect devices, data in flight and data at rest. A proper and well-planned IoT security posture might have direct implications for regulatory compliance.
Device management. One often overlooked problem is the proliferation of IoT devices. Every single IoT device must be procured, prepared, installed, connected, configured, managed, maintained and replaced or retired. It's one thing to deal with this for a few servers, but it's another problem entirely for hundreds, thousands or even tens of thousands of IoT devices. Consider the logistical nightmare involved in battery procurement and replacement for thousands of remote IoT devices. IoT leaders must employ tools and people to manage IoT devices from initial setup and configuration through monitoring, routine maintenance and disposition.
IoT security and compliance
IT and business leaders must embrace the considerations of security and compliance in any IoT deployment. IoT devices present the same basic security vulnerabilities found in any networked computer or device. The problem with IoT is volume, as there can be tens or even hundreds of thousands of IoT devices involved in an IoT deployment, each posing the same potential weaknesses that must be managed. Other security challenges include the following:
- Some IoT devices might overlook a full complement of security features or implement weak security standards, such as no default password or a default password that is well-known or easy to guess. Every IoT device must be configured to enable and use the strongest possible security features, such as strong passwords or other strong authentication techniques.
- IoT devices use little computing power by design. This can extend battery life but can make it difficult and time-consuming to update firmware and maintain IoT devices across common networks, leading to vulnerabilities that businesses are slow to address.
- IT admins must employ tools capable of discovering, configuring and monitoring all IoT devices in the deployment. Those tools must also be protected against unauthorized use or changes.
- IoT devices commonly share networks, such as Wi-Fi, with everyday users and other computing devices. This can enable attackers to easily penetrate weak IoT devices and threaten users and other devices on the shared network. It's a better practice to establish a separate network, reserved exclusively for IoT devices and protected through gateways.
IoT security can pose problems for businesses because weak default security is multiplied by countless devices that all rely on human monitoring and management efforts. The attack surface can be enormous. Thus, IoT security comes down to three principal issues:
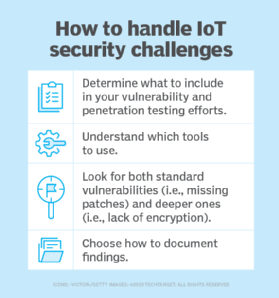
- Design. Select IoT devices with the strongest available security features, and plan to employ those strong security features from the start of any IoT design phase. Use equal care in planning and securing the corresponding IoT network environment, such as a separate Wi-Fi network for IoT devices.
- Process. Implement tools, policies and practices that successfully discover and properly configure every IoT device, including device firmware upgrades when available. No IoT devices should be left "orphaned" because they require manual configuration or other human intervention.
- Diligence. Use IoT management tools to monitor and enforce IoT device configurations, along with corresponding security tools suited for detecting intrusion or malware in IoT device deployments.
Still, IoT devices are plagued by a range of potentially devastating security risks that include botnet attacks, as well as weak DNS systems that can allow the introduction of malware, ransomware, potential attack vectors caused by unauthorized and unsecured devices on the network, and even physical threats where malicious individuals on site introduce or exploit a vulnerable IoT device or network.
Security risks carry corresponding risks to an organization's compliance posture. Imagine what happens when patient data is stolen from a medical IoT infrastructure, or a business can't manufacture products because hackers have infected the IoT infrastructure with ransomware. Such events create potential compliance headaches for business leaders and regulators. Any discussion of IoT security must include a careful evaluation of compliance.
IoT continues to evolve. There are still no common, universally adopted standards for designing, configuring, operating and securing an IoT infrastructure. In most cases, all a business can do is document design and process decisions and attempt to correlate them to other IT best practices. One example is to choose IoT devices that adhere to existing technological standards such as IPv6 and connectivity standards including Bluetooth Low Energy, Wi-Fi, Thread, Zigbee and Z-Wave. It's a good start, but it's often not enough.
Fortunately, additional compliance standards are gaining traction from industry-leading organizations, such as the IEEE. For example, the IEEE 2413-2019 standard offers a common architectural framework for IoT across transportation, healthcare, utility and other domains. It conforms to the international standard ISO/IEC/IEEE 42010:2011. Although such standards don't guarantee compliance by themselves, organizations that follow the established frameworks and practices can strengthen existing compliance postures in IoT implementation.
IoT security and compliance isn't a new or standalone issue; it demands complete and seamless alignment and integration with other IT-related compliance initiatives. Like other areas of modern IT infrastructure, IoT compliance requires addressing compliance in IoT equipment, configurations, processes and people. For example, business guidelines and best practices must be updated to include managing, using and securing IoT data. IT guidelines must be updated to reflect proper IoT configuration and monitoring of servers, storage and other IT gear.
IoT services and business models
Getting countless individual IoT devices set up can be a daunting task, but processing that data to divine useful business intelligence can bring its own problems, too. As the IoT industry evolves, the IoT ecosystem is expanding to bring new support for IoT implementation and facilitate new business models.
One of the biggest issues with IoT is simply getting it to work. Infrastructure demands can be extensive, security is often problematic, while network and processing loads can add new complexity for the business. IoT vendors are addressing these problems with a growing number of SaaS platforms designed to simplify IoT adoption and eliminate many of the deep investments needed for gateways, edge computing and other IoT-specific elements.
IoT SaaS operates between the IoT device field and the enterprise, managing many of the essential elements that an enterprise must otherwise provide. For example, the SaaS offering manages mundane infrastructure tasks, such as data security and reporting, but often includes high-level processing and computing, such as analytics, with additional support for ML. This relieves the enterprise data center from this IoT burden, and the business can focus on receiving and using the resulting analyses.
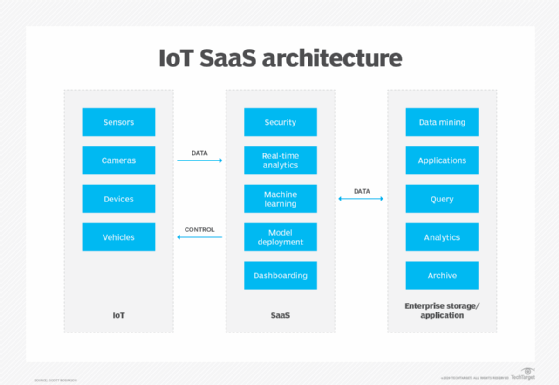
IoT SaaS offerings provide similar features, so carefully consider the pricing to select the provider best suited to the number of IoT devices, data volumes and analytical needs of your organization. Typical IoT SaaS providers include Altair SmartWorks, Emnify, Google Cloud IoT Core, IBM Watson IoT Platform, Microsoft Azure IoT Hub and Oracle Fusion Cloud IoT.
As the IoT industry expands, businesses will find that IoT tools and software are increasingly available at three principal places across the software stack:
- Devices and edge. This lowest layer of the IoT stack includes IoT device OSes, edge management platforms and data ingestion/preprocessing tools and platforms.
- Middleware. The middle of the IoT stack includes a broad array of middleware and platforms such as databases, message brokers, data ingestion and management tools, and more comprehensive IoT platforms intended to remove much of the infrastructure burden from businesses.
- Applications. The highest layer of the IoT stack includes applications such as data access, processing, reporting and visualization tools that enable businesses to work with the IoT data being collected.
IoT isn't just changing the way businesses operate; it's enabling a variety of new business models that let organizations derive revenue from IoT projects and products. Businesses are increasingly looking at ways to monetize and integrate IoT data as new growth and revenue streams. There are at least four types of business models that IoT can facilitate effectively:
- Salable data. The raw data gathered by IoT devices can readily be monetized. For example, the data gathered by a personal fitness tracker might be interesting to health insurance companies seeking to adjust rates based on consumer fitness activity and physical state, such as weight data gathered from IoT home scales.
- B2B and B2C. IoT is all about collecting and analyzing data, and such analytics can be used to identify and optimize brand loyalty or drive additional sales based on business needs or consumer activities identified by IoT devices.
- IoT platforms. The data and analytics yielded by IoT can form the foundation of platforms that offer AI services (think: Amazon's Alexa). Those platforms continue to learn and improve with a wealth of real-world IoT data, and the services offered can be integrated by third-party businesses for a fee.
- Pay-per-use. Businesses such as bicycle or scooter rentals are readily facilitated by IoT technologies. Equipment can be located by GPS, found by users with corresponding apps, and then accessed, used and paid for automatically. IoT data can analyze utilization and maintenance patterns to optimize the business process.
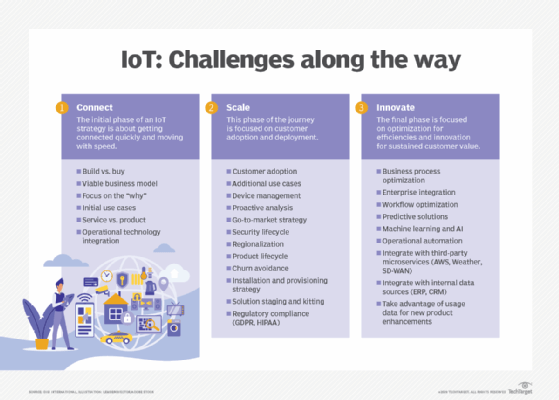
What are the requirements for implementing IoT?
There are many technical issues for IoT, including the selection and deployment of devices, network connectivity, building adequate analytical capabilities and capacity, and network and data security. But all those considerations relate to the actual building and operation of an IoT infrastructure. For many organizations, the initial questions are far simpler: Why undertake an IoT project, and how should we start?
There is no one way to approach an IoT project, and IoT initiatives can be incredibly diverse in purpose and scope. As with any IT project, an IoT initiative must start with a clear strategy that outlines the purpose of the project and clearly states its goals. Such an initial strategy might also underscore the project's intended value proposition -- such as increased productivity or decreased costs through predictive maintenance -- to justify the financial and intellectual investment required.
With a strategy in mind, the business usually moves into a period of research and experimentation to identify IoT products, software and other infrastructure elements. Project managers then implement limited proof-of-principle projects to demonstrate the technology and refine its deployment and management tactics, such as configuration and security. At the same time, analysts evaluate ways to use the resulting data and understand the tools and computing infrastructure needed to derive business intelligence from the IoT data. This might involve using limited data center resources for small-scale analytics, with an eye to public cloud resources and services as the IoT project scales.
A business can approach an IoT project in three ways:
- Experimental. Assemble a limited or test platform and then let business and technology leaders find value, similar in practice to a business starting its first test projects in a public cloud.
- Comprehensive and formal. Employ a clear project blueprint, including goals and a project timeline.
- A full commitment to IoT across the organization. Such an effort usually requires more expertise and confidence in IoT compared to others.
Regardless of the approach, the key is to remain focused on the value IoT and its data brings to the business.
What are the risks and challenges of implementing IoT?
Although the risks are well understood, the sheer volume and diversity of IoT devices requires a greater level of attention and control than a business might otherwise exercise. The most detrimental risks of IoT environments include the following:
- Inability to discover all IoT devices. IoT tools and practices must be capable of discovering and configuring all IoT devices in the environment. Undiscovered devices are unmanaged or orphaned devices that might not provide useful data and can provide attack vectors for hackers to access the network. In a broader sense, admins must be able to discover and control all IoT devices on the network.
- Weak or absent access control. IoT security depends on the proper authentication and authorization of each device. This is strengthened by each device's unique identifier, but it's still important to configure each IoT device for least privilege or zero trust, allowing access to only the network resources that are essential for IoT operation and data movement. Reinforce other security measures by adopting strong passwords and enabling network encryption for every IoT device. Default IoT passwords must be changed, and every IoT middleware, platform and application must use proper access control when communicating with IoT devices.
- Ignored or overlooked device updates. IoT devices can require periodic updates or patches to internal software or firmware. Ignoring or overlooking a device update can leave IoT devices susceptible to intrusion or hacking. Consider update planning and practices when designing an IoT environment. Some devices might be difficult or impossible to update in the field -- often because of low-bandwidth IoT network speeds -- and might even be inaccessible or problematic to take offline. These issues are a critical part of IoT device management and must be considered during the IoT project planning phase.
- Poor or weak network security. IoT deployments can add thousands of devices to a LAN. Each new device opens a potential access point for intrusion. Organizations that implement IoT often implement additional network-wide security measures, including intrusion detection and prevention systems, tightly controlled firewalls, strong data encryption and comprehensive antimalware tools. Organizations might also opt to segment the IoT network from the rest of the IT network.
- Lack of security policy or process. Policy and process are vital for proper network security. This represents the combination of tools and practices used to configure, monitor and enforce device security across the network. Proper documentation, clear configuration guidelines and rapid reporting and response are all part of IoT and everyday network security. Successful IoT policy and process are often the result of experience but should align with existing IT policy and process.
Steps for implementation
There is no single, ubiquitous approach to designing and implementing an IoT infrastructure, but there is a common suite of considerations that can help organizations check all the boxes to successfully architect and deploy an IoT project. Below are some important implementation considerations.
Network connectivity. IoT devices can offer several alternatives for connectivity, including hardwired, Wi-Fi, Bluetooth, 4G and 5G. There's no rule that requires all devices to use the same connectivity, but standardizing one approach can simplify device configuration and monitoring. Also decide whether sensors (inputs) and actuators (outputs) should use the same network or a different one that is segmented or isolated from other networks.
IoT hub. Simply passing all IoT data directly from devices to an analytics platform can result in disparate connections and poor performance. An intermediary platform, such as an IoT hub, can help organize, preprocess and encrypt data from devices across an area before sending that data along for analytics. If a remote facility is IoT-enabled, a hub might gather and preprocess that IoT data at the edge before sending it along for further analysis.
Aggregation and analytics. After the data is collected, it might drive reporting systems and actuators or be gathered for deeper analysis, query and other big data purposes. Decide on software tools used to process, analyze, visualize and drive ML. One example includes the choice of IoT database and database architectures: SQL vs. NoSQL, or static vs. streaming. These tools might be deployed in the local data center or used through SaaS platforms or cloud providers.
Device management and control. Use a software tool capable of reliably servicing all the IoT devices deployed throughout the IoT project's lifecycle. Look for high levels of automation and group/asset management capabilities to streamline configuration and reduce errors. IoT device patching and updating is emerging as a problem, and organizations should pay close attention to update and upgrade workflows.
Security. Every IoT device is a potential security vulnerability, so an IoT implementation must include a careful consideration of IoT configuration and integration into existing security tools and platforms, such as intrusion detection and prevention systems and antimalware tools. Similarly, the data produced by IoT devices will be subject to data protection, compliance and retention requirements that must be considered.
Storage and computing infrastructure. Although much of the focus is on IoT devices and support, it's critical to consider what happens to the enormous volume of data produced by the IoT infrastructure. IoT data must be stored, and then the data must be analyzed using extensive computing resources. This can sometimes involve terabytes, petabytes and even exabytes of IoT data processed through dozens -- even hundreds -- of servers configured for big data computing. The storage and computing infrastructure can be local but is increasingly relegated to public cloud providers.
What is the future of IoT?
The future of IoT can be difficult to predict because the technology and its applications are still relatively new and have enormous growth potential. Still, it's possible to make some fundamental predictions.
IoT devices will continue to proliferate, and the next few years will see billions of additional IoT devices added to the internet. As of 2023, there are more than 15 billion connected IoT devices, and this is expected to double by 2030. This growth is fueled by a combination of technologies -- including 5G connectivity -- and countless new business use cases emerging across major industries, such as healthcare and manufacturing.
Coming years will likely also see a reevaluation and increase in IoT security, starting with initial device design through business selection and implementation. Future devices will incorporate stronger security features enabled by default. A combination of new legislation, regulatory pressures and device defaults will emphasize the use of end-to-end IoT data encryption. Existing security tools, such as intrusion detection and prevention, will include support for IoT architectures with comprehensive logging and active remediation. At the same time, IoT device management tools will emphasize security auditing and automatically address IoT device security weaknesses, such as replacing traditional IoT passwords with certificate-based authentication.
In addition, some aspects of AI and IoT are converging to form a hybrid artificial intelligence of things (AIoT) technology intended to blend the data-gathering capabilities of IoT with the computing and decision-making capabilities of AI. AIoT can create a platform more capable of human-machine interaction and advanced learning capabilities. AI use cases for IoT will continue to diversify. Basic AI is already used to predict potential events, such as system failures, using real-time IoT data. Mid-tier AI will grow to provide real-time aid, such as steering assistance during driving lane deviation. And advanced AI will emerge to bring autonomy, such as adjusting a patient's insulin in response to dynamic blood glucose levels.
IoT data storage and processing at the edge will become more important as IoT device counts and data volumes place ever-greater pressure on network bandwidth and latency. This will continue to push more IoT computing work from centralized infrastructures to distributed/edge computing -- closer to where the IoT data is generated and collected.
IoT data volumes will continue to swell and translate into new revenue opportunities for businesses. That data will increasingly drive ML and AI initiatives across many industries, from science, to transportation, to finance, to retail.
Finally, the IoT marketplace will continue to grow and mature as vendors seek to offer platforms and services across the IoT stack. Cloud providers such as AWS already offer comprehensive IoT services, while telecom service providers such as AT&T have focused on IoT marketplaces where users can find varied hardware and software services for different verticals. Market maturity will help speed the creation of new IoT deployments by removing complexity and making the design and deployment process more turnkey for businesses.



